Understanding the Cyber Insurability Posture Score
Understanding the Cyber Insurability Posture Score
Understanding the CIPScore
The Cyber Insurability Posture Score (CIPScore) is Inscora's rating of how ready a client is for cyber insurance. It's built on ongoing analysis of what cyber insurers actually require, and draws on frameworks like ISO, NIST, and the Cyber Defense Matrix to identify control gaps that affect insurability.
The score combines two inputs: a discovery and perimeter scan of the client's internet-facing assets (subdomains, related domains) and the answers from the cyber insurability assessment questionnaire. The result is a carrier-agnostic score broken down across 12 control categories, each scored independently.
Note: Why these 12 controls?
These 12 categories reflect what cyber insurance carriers consistently look at when underwriting. They represent the security practices that correlate most with reduced breach likelihood and better claim outcomes. Not every insurer weighs them the same way, but these categories cover the areas carriers care about most. Strong scores here directly affect your client's ability to get good terms, pricing, and coverage.
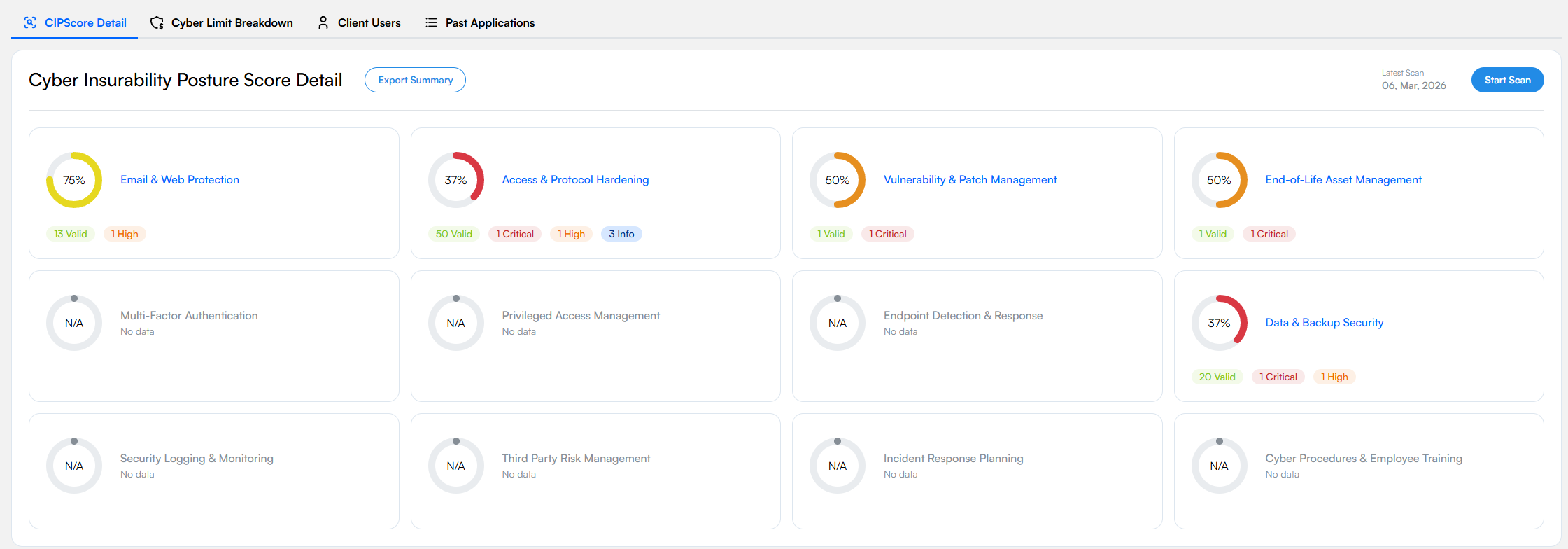
The CIPScore Detail view. Each of the 12 control categories contributes to the overall score.
The 12 Essential Control Categories
Each category card shows a percentage score, a color-coded ring, and a summary of insurability validations.
Email & Web Protection
Covers email security records (SPF, DKIM, DMARC), web content filtering, and TLS configuration. Email and web are the top attack vectors for phishing and malware, so insurers pay close attention to these controls. View all validations →
Access & Protocol Hardening
Looks at exposed services, open ports, and protocol-level security, especially remote access protocols like RDP. Unsecured remote access is one of the top entry points for ransomware, which makes it a priority for underwriters. View all validations →
Vulnerability & Patch Management
Scans for known vulnerabilities in internet-facing systems. Timely patching, especially for critical and high-severity issues, is something insurers watch closely. View all validations →
End-of-Life Asset Management
Finds systems running unsupported or end-of-life (EOL) software. These systems can't be patched against new threats and are a red flag for underwriters. View all validations →
Multi-Factor Authentication
Checks whether MFA is enforced across exposed services, remote access, privileged accounts, and critical systems. Many carriers now treat MFA as a minimum requirement, since compromised credentials are involved in a large share of cyber incidents.
Privileged Access Management
Reviews who has elevated permissions, how those permissions are managed, and whether endpoint privilege management is in place. Limiting privileged access reduces the damage from a compromised account, which insurers view favorably.
Endpoint Detection & Response
Looks at EDR deployment across workstations, laptops, and servers. Insurers care not just about whether EDR is in place, but how much of the environment it actually covers. Partial deployment leaves gaps.
Data & Backup Security
Covers backup configurations and data protection: are backups encrypted, tested regularly, and stored offline? In a ransomware scenario, viable backups can be the difference between a full recovery and paying the ransom. View all validations →
Security Logging & Monitoring
Covers security event logging, SIEM, SOC operations, and alerting. Good monitoring means faster breach detection. This category looks at things like account lockout policies, audit log analysis, and SOC/MSSP coverage.
Third Party Risk Management
Looks at how the client manages cyber risks from vendors and supply chain partners. A breach at a third party can directly impact the client, so insurers want to see that vendor security is actively monitored.
Incident Response Planning
Does the client have a documented incident response plan? Do they run tabletop exercises? Do they have retainer agreements with IR providers? Organizations with tested response plans consistently see better outcomes when breaches happen.
Cyber Procedures & Employee Training
Covers security policies, procedures, and employee awareness training, including phishing simulations. Human error is still one of the top causes of cyber incidents. Frequent, quality training (not just the annual compliance checkbox) leads to measurably lower breach rates.
Note: Perimeter scan vs. full CIPScore
The perimeter scan only scores categories it can assess from the outside (Email & Web Protection, Access & Protocol Hardening, Vulnerability & Patch Management, End-of-Life Asset Management). The rest (MFA, Incident Response, Employee Training, etc.) need input from the client through the cyber insurability assessment , a guided questionnaire you can drive from the platform.
Severity Levels
Within each category, individual insurability validations are tagged by severity. These levels indicate the impact on your client's cyber insurability posture:
Severity | Description |
|---|---|
🔴 Critical | Major issues that may prevent your client from getting cyber insurance. |
🟠 High | Issues that could impact premiums or renewal terms. |
🟡 Medium | General cyber risks that might not affect insurability but should still be addressed. |
🟤 Low | Minor issues with limited known impact, but worth monitoring. |
🟢 Valid | Positive indicators that improve your client's insurability. |
🔵 Info | Informational items for discussion with the insurer or broker. |
N/A Categories
Some categories may show N/A / "No data." This means the perimeter scan can't assess that area from the outside (e.g. internal MFA policies, incident response plans, employee training). These categories need client input, which is why inviting a client user and completing the assessment are important next steps.
Understanding Your Scan Results with Explain
Every validation group in the CIPScore detail view has an Explain button. Click it to open a side panel with an AI-generated briefing tailored to your client's specific situation: what was found, why it matters for insurability, how to fix it, and how your services connect to the solution.
To understand what any insurability validation means, how it affects your client's posture, or what to do about it, use the Explain button directly on that validation. Each briefing is generated from your client's actual data and is always current with their latest scan. See The Explain Feature for a full walkthrough of what the Explain panel contains.
Tip: Explain before you interpret
Before discussing scan results with a client or trying to interpret what a validation means, click the Explain button on that validation. The briefing covers the technical meaning, insurability impact, real-world incident references, step-by-step remediation, and how your own services connect to the solution. It's the most complete and accurate way to understand any scan result.
Export Summary
Once a scan has completed, you can generate a Cyber Insurability Report directly from the platform. On the CIPScore Detail tab, click the Export Summary button. Inscora compiles the scan results, category scores, and insurability validations into a downloadable PDF.
Click Export Summary to generate the report. Once ready, use the download icon next to "Latest Report" to download the PDF.
The report is meant to be shared with clients, brokers, and internal stakeholders. It gives a branded summary of the client's cyber insurability posture (category scores, severity breakdowns, key scan results) without requiring anyone to log in.
Tip: Prospecting with the report
The Export Summary works well for prospecting. Run a scan, export it, and use it as a conversation starter with potential clients: here's your current exposure, here's how we can help. It turns a technical scan into a business document you can hand to someone.
View a sample Cyber Insurability Report
Here is an example of what the exported report looks like:
The report includes the Inscora branding, CIPScore overview, individual category results, severity-coded validations, and methodology references. The exact content will vary based on the client's scan results.